I got a notification from Kaspersky IS about a clr.exe infected file residing in the path "C:\Users[i]username[/i]\AppData\Local\Temp", there was also a running process associated with it, I have no idea how that happened and got passed KIS, anyways the annoying part was that KIS was not able to disinfect (delete) even with a reboot. While I was doing that manually, the files CLR.exe, CLR.bat, and CLR.txt kept being created on reboot, so I used sysinternals procmon.exe to check the process activity. While I was at it I displayed the process tree and noticed :
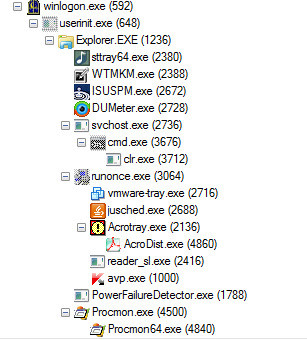
The interesting part here is that this svchost.exe residing in "c:\Users[i]username[/i]\AppData\Roaming\Microsoft" is not detected by Kaspersky and it is the parent process that creates the CLR.exe file and runs it on reboot, even scanning the file manually does not raise any flags. I finally did the removal manually, now going to change passwords since I am not sure what was uploaded by this trojan.
Anyone has any idea about this or has experienced a similar situation, please share...